This article supports the broader framework explained in the main guide:
Security Patrol Science — The 5 Principles of Modern Guard OperationsThis supporting article focuses on security guard accountability, patrol system manipulation, RFID guard tour weaknesses, and why modern patrol verification requires tamper-resistant, real-time operational evidence.

Security Patrol Science • Security Guard Accountability, Patrol Verification, and Operational Proof
Security Guard Accountability: When Patrol Systems Can Be Manipulated
One of the most dangerous misconceptions in the security industry is the belief that if a system records patrol activity, the patrol must have actually happened. In reality, security guard accountability depends on whether patrol activity can be verified, not merely logged.
When Patrol Systems Create a False Sense of Security
One of the most dangerous misconceptions in the security industry is the belief that if a system records patrol activity, the patrol must have actually happened.
As a former police commander and security operations specialist, I have seen many cases where the opposite was true. A system may generate logs, timestamps, and reports — yet the patrol itself never took place.
Without true operational accountability, recorded data can easily become a very convincing lie.
One case in particular illustrates this problem with painful clarity.
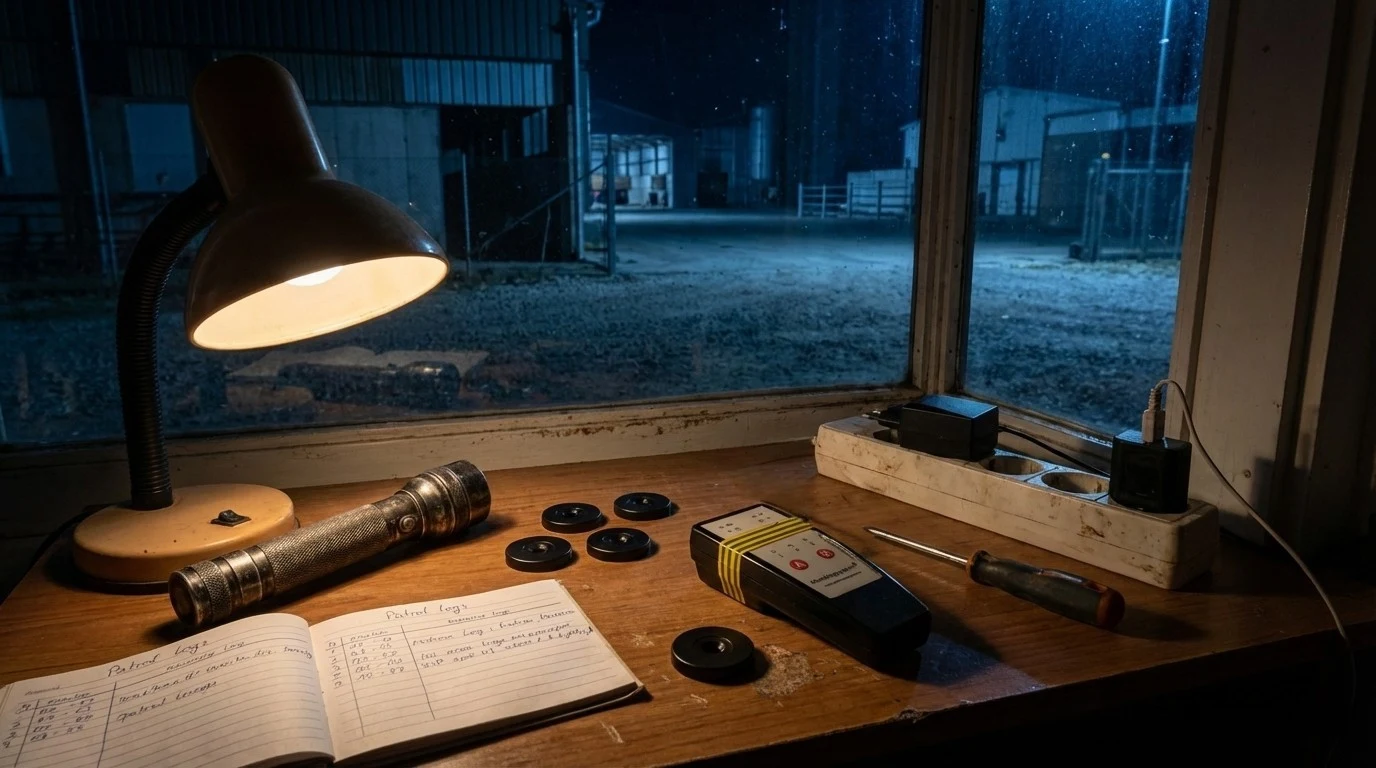
The Livestock Facility Case
Several years ago I was involved in an investigation at a large livestock facility.
The site protected valuable cattle stock and covered a wide operational area. A private security company was responsible for guarding the property around the clock.
Management believed the site was well protected. After all, the security contractor had installed a “modern” patrol verification system using a traditional RFID guard tour system with checkpoint discs.
According to the daily reports, the guards completed their patrol routes with perfect precision every night. The logs showed checkpoints scanned exactly on schedule, suggesting a highly disciplined patrol routine.
Because of these seemingly perfect reports, the security company’s supervisors rarely performed physical inspections on the site.
On paper, everything looked flawless.
In reality, the property was almost completely unprotected.
During my years supervising patrol operations, I repeatedly observed how patrol verification systems could be manipulated when they lacked location verification and real-time monitoring.
How Guards Manipulated the RFID Patrol System
The guards quickly discovered a fundamental weakness in the system.
The RFID-based patrol checkpoints operated entirely offline. The system recorded that a checkpoint was scanned — but it had no way to verify where the scan actually occurred.
At the beginning of their shifts, the guards simply removed the checkpoint discs from the remote buildings using a screwdriver. They carried the discs back to the heated guard shack.
Throughout the night, they never left the building.
Instead, they scanned the discs from inside the shack at the required times, generating what appeared to be perfectly executed patrol records.
At the end of the shift, they returned the discs to their original locations — assuming they were not simply handing them over to the next shift.
From the system’s perspective, the patrol had been completed flawlessly.
In reality, the facility remained completely unguarded for entire nights.
- offline checkpoint scanning
- removable RFID discs
- no location verification
- no supervisor visibility
When the Failure Became Visible
Eventually, the inevitable happened.
During a weekend night shift, intruders entered the property.
They cut through the fence at the section farthest from the guard post — exactly the area that should have been inspected during patrol rounds.
Several valuable cattle were stolen, resulting in significant financial losses for the facility.
When the incident was reported, the guards insisted that they had been performing patrols throughout the night.
The patrol logs appeared to support their claims.
However, once the investigation began and the personnel were formally questioned, the truth became clear.
Not once during that weekend shift had the guards left the guard shack.
The patrol system had recorded a complete patrol schedule — yet the patrol itself had never occurred.
The Cost of Delayed Reporting
The situation became even worse due to a delay in reporting the incident.
The facility workers noticed the missing animals on Sunday. However, they hesitated to report the problem to management, fearing internal consequences.
The theft was only officially reported on Monday.
By that time, the delay combined with the false patrol records had severely compromised the investigation.
Critical evidence had already disappeared. The time gap made it extremely difficult to reconstruct events or identify the perpetrators.
The combination of a manipulated patrol system and delayed reporting turned a solvable case into a nearly impossible one.
Why Traditional Guard Tour Systems Fail
The problem was not the guards alone.
The system itself allowed the manipulation.
Any patrol verification technology that does not confirm the physical location of the guard is vulnerable to this type of abuse.
Without real-time verification, patrol records can easily become administrative fiction rather than operational evidence.
Guard tour systems that rely only on offline checkpoint scans cannot guarantee patrol integrity.
Patrol verification checkpoints only matter when the system can prove where the checkpoint was scanned.
What Real Patrol Accountability Requires
True patrol accountability depends on verifiable operational data.
Modern patrol verification systems solve this problem through several key mechanisms:
- GPS patrol tracking
- real-time patrol monitoring
- patrol route history
- tamper-resistant checkpoints
- incident report verification
These features create what security professionals refer to as a security patrol audit trail — a verifiable timeline of patrol activity that cannot be easily falsified.
When such systems are in place, supervisors can confirm not only that a checkpoint was scanned, but also where and when the patrol actually occurred.
Patrol verification systems must confirm both time and location to provide real accountability.
Real-time patrol monitoring is essential for modern security operations.
The Accountability Principle in Modern Security Operations
Technology alone does not guarantee security.
What matters is whether the technology produces verifiable, tamper-resistant operational evidence.
True security guard accountability begins when patrol activity can be independently confirmed through reliable operational data.
This is the accountability principle at the heart of modern patrol verification: security work must be measurable, reconstructable, and defensible when something goes wrong.
The lesson is simple: if your patrol system can be manipulated from inside a guard shack, it is not protecting your site. Real security accountability begins where verifiable operational proof replaces assumption, memory, and paperwork.
This article is part of the broader Security Patrol Science framework , which explains the five core principles behind modern patrol verification systems.
See How Trinity Guard® Helps Prevent Patrol Manipulation
If your current patrol process still depends on trust, paper logs, or offline checkpoint scans, explore how Trinity Guard® combines GPS patrol tracking, route history, live monitoring, and audit-ready evidence in one operational system.
- Security Guard Accountability: Patrol activity must be proven, not merely reported.
- RFID Weakness: Offline guard tour systems can be manipulated when scans are detached from real location.
- Operational Risk: False patrol records delay investigations and weaken incident response.
- Modern Standard: GPS patrol tracking and live monitoring create real patrol integrity.
- Audit Trail Logic: Reliable security operations depend on tamper-resistant, reconstructable records.
Gyula Györfi is a security operations specialist with more than two decades of experience in law enforcement and private security supervision. He has investigated patrol failures, reconstructed field activity, and analyzed how weak patrol verification systems can create false accountability.
He is the founder of Trinity Guard®, an AI-assisted patrol verification platform designed to bring tamper-resistant route history, live monitoring, and defensible operational proof into modern security patrol management.